I will provide a couple solutions to tutorial #9′s homework assignment. Keep in mind that there are an infinite amount of ways to crack this app, and this is only a small sample. If you found a way to do it on your own, congratulations. If not, don’t worry, we’ll be covering it all many times.
Solution #1
One of the easiest ways to patch the app is to simple NOP out the JNZ instruction at address 40129F:
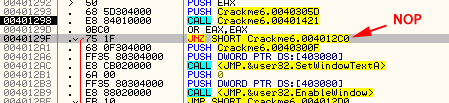
This will force the app to fall through to the good message every time.
Solution #2
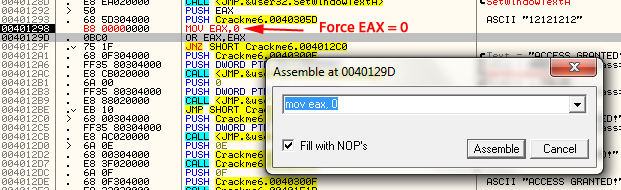
Another possibility is to make sure EAX always equals zero is simply replacing the call to check the password with a MOV EAX, 0:
This basically removes the entire call to check the password’s validity and always jumps to the good boy ![]() .
.
Solution #3
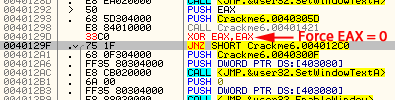
Following the same line of reasoning as #2 above, we could keep the call, but right after it returns we can then force EAX to always equal zero. Just replace the OR EAX,EAX with an XOR EAX, EAX:
I like this solution as there’s a certain irony to it (you’re only patching one byte and your only adding one letter ![]() ).
).
Extra Credit
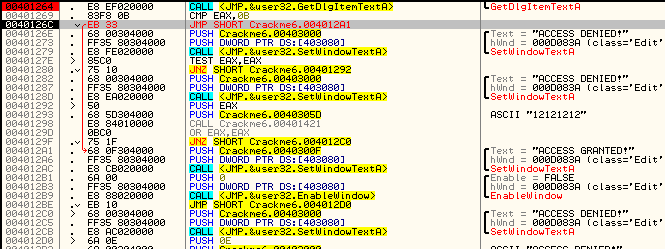
I hope you didn’t fret too much about the extra credit problem. The simplest way to remove the restriction on the password length is just to replace the original jump if the password was too long and replace it with a jump directly to the good boy message.
This is rather hackish (and we’ll see in the next tutorial that there are far better ways) but it does work. This has the benefit of not only patching the app to always accept your password, but unlike the solutions above, it also removes any restrictions on what that password should be.
July 17th, 2012 on 6:22 pm
About the Count parameter = C (12.) in GetDlgItemTextA (PUSH 0C)… what if we nop it? Do we cause any implication in the function? Is there a value so we can set C (12) to infinite?
July 18th, 2012 on 2:52 am
First , let me say that you should probably post on the forum as a lot more people will read your questions and you’ll get answers faster, but that being said…
NOPing the push will probably crash, depending on what’s on the stack as the function call will POP these arguments off, but since you have not pushed the 0x0C argument, it will pull the next thing off the stack- probably the return address. As soon as you hit a RETN statement, you will be off to la la land.
You could set the 0x0C value to 0xFE, which will raise it to 255 digits, but there is nothing you could put in to give an infinite amount.
July 18th, 2012 on 5:15 pm
Forums it is then. Thanks.
July 24th, 2012 on 6:32 am
The way I solved this is very similar to your solution #3, except I changed the OR EAX, EAX to CMP EAX, EAX. I like the XOR EAX, EAX though. It never occurred to me that it would force the register to be 0. Thanks for the tutorials; they’re great!
April 20th, 2013 on 5:21 am
I changed address 0040126C from “JB SHORT Crackme6.0040127E” to “JMP SHORT Crackme6.004012A1″ thus going to “good boy” regardless if it was right or above 11 characters.
July 30th, 2013 on 8:30 am
XOR EAX,EAX allows a length longer than 11chars too, that was the only thing i changed and worked fine.