Zer0Flag, an official friend of the Legend of Random site, has released a new plugin for OllyDBG 2.0 called OllyCallstack. From the author:
“Just wanted to get into the development of OllyDbg Plugins and displaying the call stack is a feature that I missed in Olly 2.x so I wrote a little Plugin which offers some basic information about the call stack.”
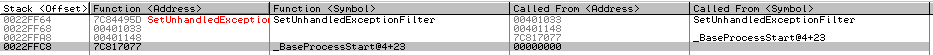
(Click on picture to view larger image)
“The Function at the top is always the last called and a double click on a row brings you to the disassembly view with the selected address. But you need a target loaded and it must be in suspended mode else the window won´t show you the call stack. Also it doesn´t update when you step while having the window of the Plugin open so you need to press the Plugin function in your menu again to update the view.
Plugin + Source is in the attachment – Tested with OllyDbg 2.01b2 on WinXP SP3 and Win7 SP1″
The plugin is available on the tools page. Any comments, suggestions or questions? Leave a comment here and Zer0Flag will be checking this page, answering questions and what-not. Nice going Zer0Flag, and keep up the good work.