Unfortunately, our lives as reverse engineers is not always easy. If all it took to patch an app was a deleted resource or a quick patch, a lot more people would do it. Sometimes we must get a little ‘low-level’, wallow around in the operating system files, single-step an exception handler, or reverse engineer an unknown packer. To have a well-rounded skill set as a cracker, we must know a lot about a lot (or at least where to look about a lot) and it can get pretty technical.
This tutorial is about one of those technical areas: TLS callbacks. It is not easy, nor is it simple, but it can ruin an otherwise nice day of a reverse engineer that doesn’t at least understand the basics of what they are, when they are used, and how to overcome them.
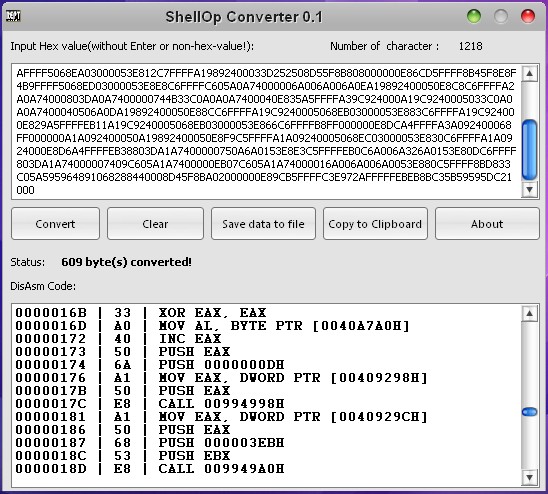
As in all tutorials on my site, the required files are included in the download of this tutorial on the tutorials page. We will be looking at three binaries, all included. We will also be using an Olly plugin called TLSCatch by Walliedassar, also included. Lastly, we will be using CFF Explorer, available on the tools page.
(continue reading…)